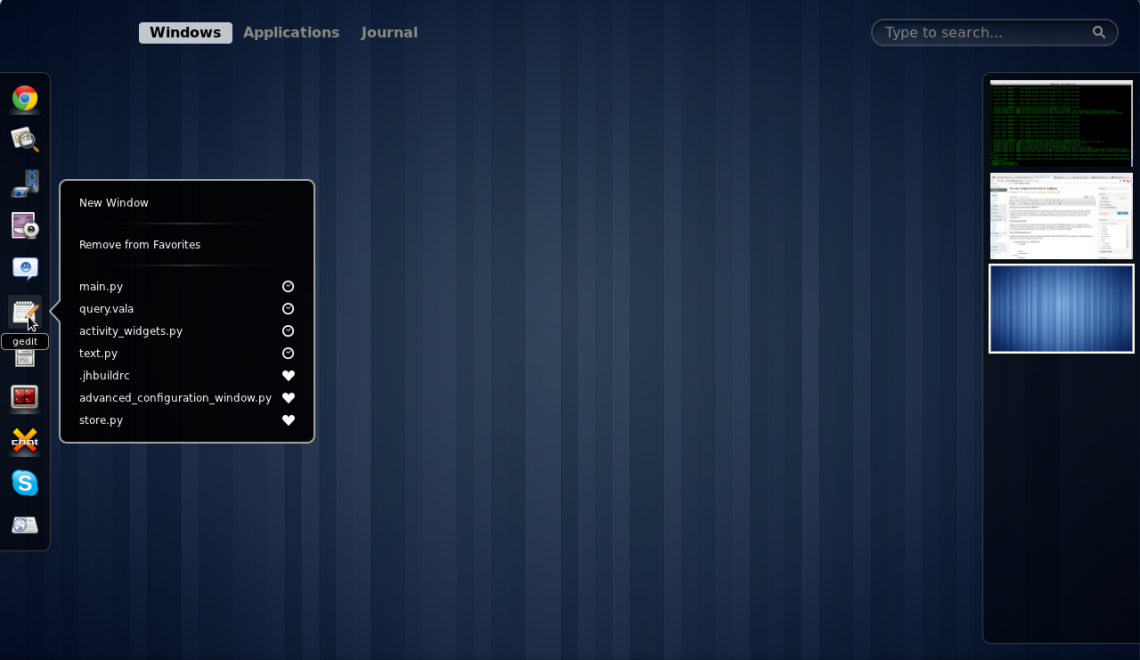
GNOME Shell Extensions that Improve the Interface
We have GNOME 3.0 now and it introduced a new overview mode. Now you can launch apps, switch between windows, and also managed virtual desktops. I loved it, and GNOME easily became my favorite desktop environment on any OS. But there are a few changes I would like to make and I can, this is one of the greatest about GNOME. You can change things to to your choice if you don’t like the default experience.